Meltdown and Spectre: The Flaws in Every Computer Chip

Yesterday, security researchers publicly disclosed two vulnerabilities that affect virtually every computer processor manufactured in the last two decades. They're called Meltdown and Spectre, and they're unlike anything we've seen before.
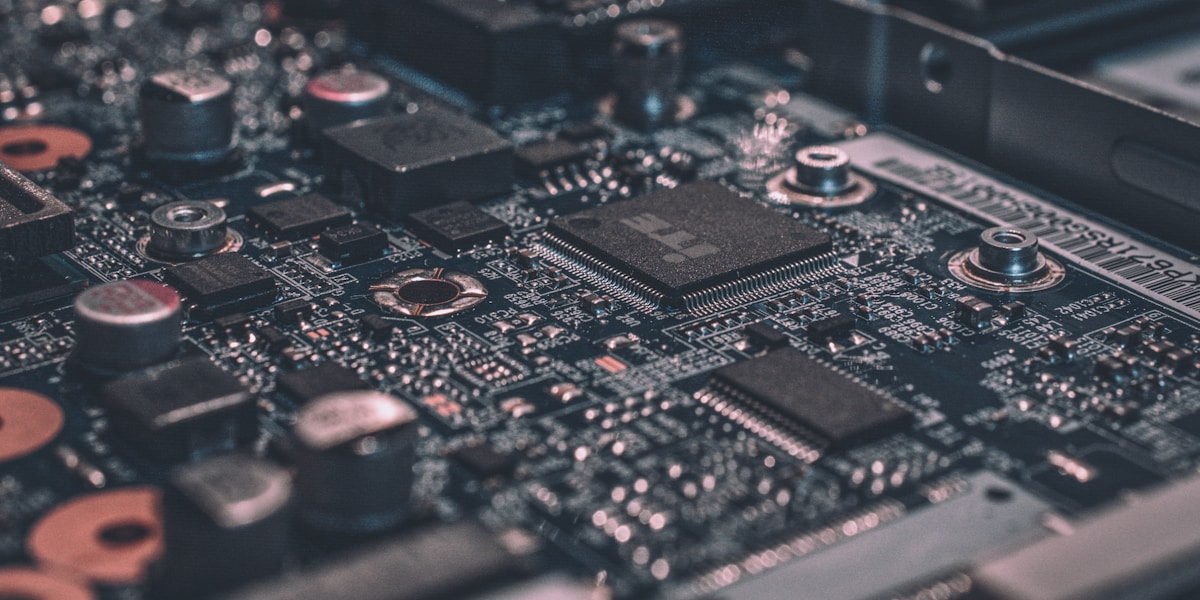
Unlike WannaCry or NotPetya, which exploited software bugs, these flaws are in the hardware itself. In the physical design of Intel, AMD, and ARM processors. They can't be fully fixed without replacing the chips. Software patches mitigate the risk but may impact performance.
Take a breath. Let's walk through this calmly.
What They Are
Meltdown (CVE-2017-5754)
Meltdown breaks the fundamental isolation between applications and the operating system. It allows a program to read data from the operating system's kernel memory, which can contain passwords, encryption keys, and other sensitive data. It primarily affects Intel processors.
Spectre (CVE-2017-5753, CVE-2017-5715)
Spectre breaks the isolation between different applications. It tricks programs into leaking data from their memory. It affects Intel, AMD, and ARM processors, which means virtually every computer, phone, tablet, and server on the planet. Spectre is harder to exploit but also harder to patch.
How Serious Is This?
On the severity scale, this is a 10 out of 10 in terms of scope: every computer is affected. But in terms of practical risk to your practice right now, it's more moderate:
- There are no known real-world exploits yet (these are proof-of-concept attacks by researchers)
- Exploiting these flaws requires running malicious code on the target machine
- The most likely attack vector is through a web browser (malicious JavaScript)
- Patches are already available or coming soon for all major operating systems
What to Do
Update Everything (Again)
- Windows: Emergency update released January 3rd. Apply immediately. Note: some antivirus software is incompatible and may cause blue screens. Check with your AV vendor before applying.
- macOS: Apple partially patched in macOS 10.13.2 (December). Additional patches coming in 10.13.3.
- iOS: Patched in iOS 11.2.
- Android: January security patch addresses the issue. Availability depends on your device manufacturer.
- Browsers: Chrome, Firefox, and Edge are releasing updates to mitigate browser-based attacks. Update your browsers immediately.
Performance Impact
The Meltdown patches work by changing how the processor handles memory access. This adds overhead, which means some slowdown. Early benchmarks show:
- Consumer workloads (email, browsing, office apps): minimal impact (2-5%)
- Server workloads with heavy I/O: potentially significant impact (5-30%)
- Older processors: more impact than newer ones
For a dental practice running Dentrix or Open Dental, the performance impact should be minimal. For servers handling heavy database loads, monitor performance after patching.
Firmware Updates
Intel is releasing microcode updates that further mitigate Spectre. These will come through BIOS/firmware updates from your computer manufacturer (Dell, HP, Lenovo, etc.). Check for firmware updates in the coming weeks and apply them.
The Bigger Picture
Meltdown and Spectre represent a new category of vulnerability: hardware flaws that software can only partially mitigate. They'll influence processor design for years to come. Future chips will be designed with these attack techniques in mind.
For now: patch, update browsers, and don't panic. The researchers who discovered these flaws followed responsible disclosure, and the industry had months to prepare patches before the public announcement. The system worked.